[ad_1]
On this publish, we present you learn how to apply attribute-based entry management (ABAC) whilst you retailer and handle your Amazon Elastic Kubernetes Providers (Amazon EKS) workload secrets and techniques in AWS Secrets and techniques Supervisor, after which retrieve them by integrating Secrets and techniques Supervisor with Amazon EKS utilizing Exterior Secrets and techniques Operator to outline extra fine-grained and dynamic AWS Identification and Entry Administration (IAM) permission insurance policies for accessing secrets and techniques.
It’s widespread to handle quite a few workloads in an EKS cluster, every necessitating entry to a definite set of secrets and techniques. You possibly can confirm adherence to the precept of least privilege by creating separate permission insurance policies for every workload to limit their entry. To scale and cut back overhead, Amazon Net Providers (AWS) recommends utilizing ABAC to handle workloads’ entry to secrets and techniques. ABAC helps cut back the variety of permission insurance policies wanted to scale together with your surroundings.
What’s ABAC?
In IAM, a conventional authorization strategy is called role-based entry management (RBAC). RBAC units permissions based mostly on an individual’s job operate, generally often called IAM roles. To implement RBAC in IAM, distinct insurance policies for varied job roles are created. As a greatest apply, solely the minimal permissions required for a particular function are granted (precept of least privilege), which is achieved by specifying the sources that the function can entry. A limitation of the RBAC mannequin is its lack of flexibility. Each time new sources are launched, you need to modify insurance policies to allow entry to the newly added sources.
Attribute-based entry management (ABAC) is an strategy to authorization that assigns permissions in accordance with attributes, which within the context of AWS are known as tags. You create and add tags to your IAM sources. You then create and configure ABAC insurance policies to allow operations requested by a principal when there’s a match between the tags of the principal and the useful resource. When a principal makes use of short-term credentials to make a request, its related tags come from session tags, incoming transitive periods tags, and IAM tags. The principal’s IAM tags are persistent, however session tags, and incoming transitive session tags are short-term and set when the principal assumes an IAM function. Observe that AWS tags are connected to AWS sources, whereas session tags are solely legitimate for the present session and expire with the session.
How Exterior Secrets and techniques Operator works
Exterior Secrets and techniques Operator (ESO) is a Kubernetes operator that integrates exterior secret administration techniques together with Secrets and techniques Supervisor with Kubernetes. ESO supplies Kubernetes customized sources to increase Kubernetes and combine it with Secrets and techniques Supervisor. It fetches secrets and techniques and makes them out there to different Kubernetes sources by creating Kubernetes Secrets and techniques. At a fundamental stage, it’s worthwhile to create an ESO SecretStore useful resource and a number of ESO ExternalSecret sources. The SecretStore useful resource specifies learn how to entry the exterior secret administration system (Secrets and techniques Supervisor) and means that you can outline ABAC associated properties (for instance, session tags and transitive tags).
You declare what knowledge (secret) to fetch and the way the info ought to be reworked and saved as a Kubernetes Secret within the ExternalSecret useful resource. The next determine reveals an outline of the method for creating Kubernetes Secrets and techniques. Later on this publish, we assessment the steps in additional element.
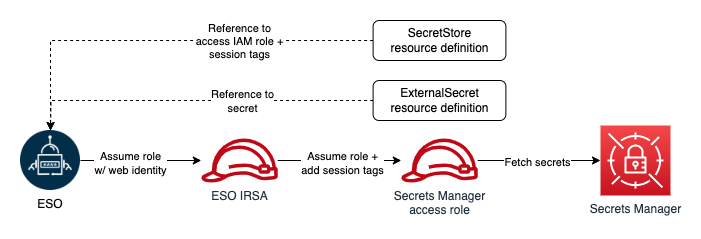
Determine 1: ESO course of
Easy methods to use ESO for ABAC
Earlier than creating any ESO sources, you need to be sure that the operator has adequate permissions to entry Secrets and techniques Supervisor. ESO affords a number of methods to authenticate to AWS. For the aim of this resolution, you’ll use the controller’s pod identification. To implement this methodology, you configure the ESO service account to imagine an IAM function for service accounts (IRSA), which is utilized by ESO to make requests to AWS.
To stick to the precept of least privilege and confirm that every Kubernetes workload can entry solely its designated secrets and techniques, you’ll use ABAC insurance policies. As we talked about, tags are the attributes used for ABAC within the context of AWS. For instance, principal and secret tags could be in comparison with create ABAC insurance policies to disclaim or enable entry to secrets and techniques. Secret tags are static tags assigned to secrets and techniques symbolizing the workload consuming the key. Alternatively, principal (requester) tags are dynamically modified, incorporating workload particular tags. The one viable choice to dynamically modifying principal tags is to make use of session tags and incoming transitive session tags. Nonetheless, as of this writing, there isn’t any method so as to add session and transitive tags when assuming an IRSA. The workaround for this concern is function chaining and passing session tags when assuming downstream roles. ESO affords function chaining, that means which you can consult with a number of IAM roles with entry to Secrets and techniques Supervisor within the SecretStore useful resource definition, and ESO will chain them with its IRSA to entry secrets and techniques. It additionally means that you can outline session tags and transitive tags to be handed when ESO assumes the IAM roles with its major IRSA. The flexibility to move session tags means that you can implement ABAC and examine principal tags (together with session tags) with secret tags each time ESO sends a request to Secrets and techniques Supervisor to fetch a secret. The next determine reveals ESO authentication course of with function chaining in a single Kubernetes namespace.
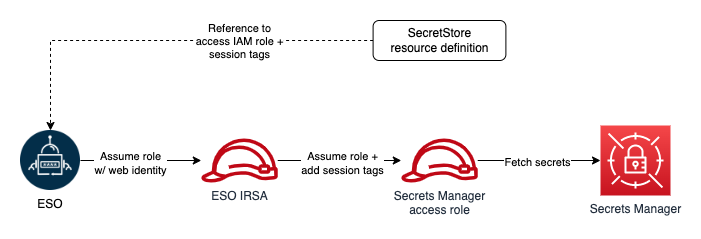
Determine 2: ESO AWS authentication course of with function chaining (single namespace)
Structure overview
Let’s assessment implementing ABAC with a real-world instance. When you may have a number of workloads and companies in your Amazon EKS cluster, every service is deployed in its personal distinctive namespace, and repair secrets and techniques are saved in Secrets and techniques Supervisor and tagged with a service title (key=service, worth=service title). The next determine reveals the required sources to implement ABAC with EKS and Secrets and techniques Supervisor.
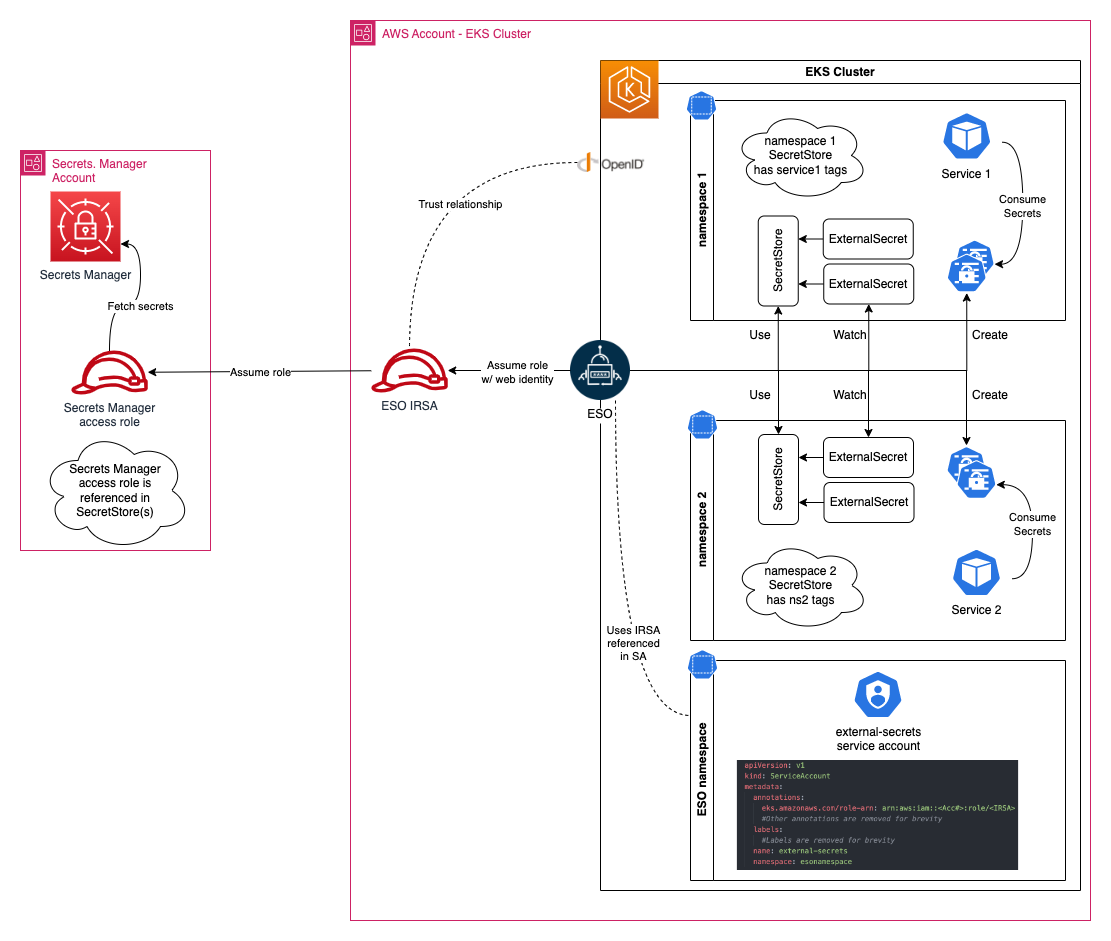
Determine 3: Amazon EKS secrets and techniques administration with ABAC
Conditions
Deploy the answer
Start by putting in ESO:
From a terminal the place you normally run your helm instructions, run the next helm command so as to add an ESO helm repository.
Set up ESO utilizing the next helm command in a terminal that has entry to your goal Amazon EKS cluster:
To confirm ESO set up, run the next command. Be sure you move the identical namespace because the one you used when putting in ESO:
See the ESO Getting began documentation web page for extra info on different set up strategies, set up choices, and learn how to uninstall ESO.
Create an IAM function to entry Secrets and techniques Supervisor secrets and techniques
You could create an IAM function with entry to Secrets and techniques Supervisor secrets and techniques. Begin by making a buyer managed coverage to connect to your function. Your coverage ought to enable studying secrets and techniques from Secrets and techniques Supervisor. The next instance reveals a coverage which you can create to your function:
Contemplate the next on this coverage:
Secrets and techniques Supervisor makes use of an AWS managed key for Secrets and techniques Supervisor by default to encrypt your secrets and techniques. It’s beneficial to specify one other encryption key throughout secret creation and have separate keys for separate workloads. Modify the useful resource aspect of the second coverage assertion and substitute <KMS Key ARN> with the KMS key ARNs used to encrypt your secrets and techniques. If you happen to use the default key to encrypt your secrets and techniques, you’ll be able to take away this assertion.
The coverage assertion conditionally permits entry to all secrets and techniques. The situation aspect permits entry solely when the worth of the principal tag, recognized by the important thing service, matches the worth of the key tag with the identical key. You possibly can embrace a number of situations (in separate statements) to match a number of tags.
After you create your coverage, comply with the information for Creating IAM roles to create your function, attaching the coverage you created. Use the default worth to your function’s belief relationship for now, you’ll replace the belief relationship within the subsequent step. Observe the function’s ARN after creation.
Create an IAM function for the ESO service account
Use eksctl to create the IAM function for the ESO service account (IRSA). Earlier than creating the function, you need to create an IAM coverage. ESO IRSA solely wants permission to imagine the Secrets and techniques Supervisor entry function that you just created within the earlier step.
Use the next instance of an IAM coverage which you can create. Substitute <Secrets and techniques Supervisor Entry Position ARN> with the ARN of the function you created within the earlier step and comply with making a buyer managed coverage to create the coverage. After creating the coverage, observe the coverage ARN.
Subsequent, run the next command to get the account title of the ESO service. You will note an inventory of service accounts, decide the one which has the identical title as your helm launch, on this instance, the service account is external-secrets.
Subsequent, create an IRSA and configure an ESO service account to imagine the function. Run the next command to create a brand new function and affiliate it with the ESO service account. Substitute the variables in brackets (<instance>) together with your particular info:
You possibly can validate the operation by following the steps listed in Configuring a Kubernetes service account to imagine an IAM function. Observe that you just needed to move the ‑‑override-existing-serviceaccounts argument as a result of the ESO service account was already created.
After you’ve validated the operation, run the next command to retrieve the IRSA ARN (substitute <IRSA title> with the title you used within the earlier step):
Modify the belief relationship of the function you created beforehand and restrict it to your newly created IRSA. The next ought to resemble your belief relationship. Substitute <IRSA Arn> with the IRSA ARN returned within the earlier step:
Observe that you may be utilizing session tags to implement ABAC. When utilizing session tags, belief insurance policies for all roles related to the identification supplier (IdP) passing the tags should have the sts:TagSession permission. For roles with out this permission within the belief coverage, the AssumeRole operation fails.
Furthermore, the situation block of the second assertion limits ESO’s capacity to move session tags with the important thing title ekssecret. We’re utilizing this situation to confirm that the ESO function can solely create session tags used for accessing secrets and techniques supervisor, and doesn’t achieve the power to set principal tags that could be used for some other objective. This fashion, you’re making a namespace to assist stop additional privilege escalations or escapes.
Create secrets and techniques in Secrets and techniques Supervisor
You possibly can create two secrets and techniques in Secrets and techniques Supervisor and tag them.
Observe the steps in Create an AWS Secrets and techniques Supervisor secret to create two secrets and techniques named service1_secret and service2_secret. Add the next tags to your secrets and techniques:
service1_secret:
key=ekssecret, worth=service1
service2_secret:
key=ekssecret, worth=service2
Run the next command to confirm each secrets and techniques are created and tagged correctly:
Create ESO objects in your cluster
Create two namespaces in your cluster:
Assume that service1-ns hosts service1 and service2-ns hosts service2. After creating the namespaces to your companies, confirm that every service is restricted to accessing secrets and techniques which are tagged with a particular key-value pair. On this instance the important thing ought to be ekssecret and the worth ought to match the title of the corresponding service. Which means that service1 ought to solely have entry to service1_secret, whereas service2 ought to solely have entry to service2_secret. Subsequent, declare session tags in SecretStore object definitions.
Edit the next command snippet utilizing the textual content editor of your alternative and substitute each occasion of <Secrets and techniques Supervisor Entry Position ARN> with the ARN of the IAM function you created earlier to entry Secrets and techniques Supervisor secrets and techniques. Copy and paste the edited command in your terminal and run it to create a .yaml file in your working listing that incorporates the SecretStore definitions. Be sure that to alter the AWS Area to mirror the Area of your Secrets and techniques Supervisor.
Create SecretStore objects by operating the next command:
Validate object creation by operating the next command:
Examine the standing and occasions part for every object and ensure the shop is validated.
Subsequent, create two ExternalSecret objects requesting service1_secret and service2_secret. Copy and paste the next command in your terminal and run it. The command will create a .yaml file in your working listing that incorporates ExternalSecret definitions.
Run the next command to create objects:
Confirm the objects are created by operating following command:
Every ExternalSecret object ought to create a Kubernetes secret in the identical namespace it was created in. Kubernetes secrets and techniques are accessible to companies in the identical namespace. To exhibit that each Service A and Service B has entry to their secrets and techniques, run the next command.
It’s best to see service1-ns-secret1 created in service1-ns namespace which is accessible to Service 1, and service1-ns-secret2 created in service2-ns which is accessible to Service2.
Attempt creating an ExternalSecrets object in service1-ns referencing service2_secret. Discover that your object reveals SecretSyncedError standing. That is the anticipated habits, as a result of ESO passes completely different session tags for ExternalSecret objects in every namespace, and when the tag the place key’s ekssecret doesn’t match the key tag with the identical key, the request will probably be rejected.
What about AWS Secrets and techniques and Configuration Supplier (ASCP)?
Amazon affords a functionality known as AWS Secrets and techniques and Configuration Supplier (ASCP), which permits purposes to devour secrets and techniques instantly from exterior shops, together with Secrets and techniques Supervisor, with out modifying the applying code. ASCP is actively maintained by AWS, which makes certain that it stays updated and aligned with the most recent options launched in Secrets and techniques Supervisor. See Easy methods to use AWS Secrets and techniques & Configuration Supplier together with your Kubernetes Secrets and techniques Retailer CSI driver to be taught extra about learn how to use ASCP to retrieve secrets and techniques from Secrets and techniques Supervisor.
At present, prospects who use AWS Fargate with Amazon EKS can’t use the ASCP methodology as a result of incompatibility of daemonsets on Fargate. Kubernetes additionally doesn’t present a mechanism so as to add particular claims to JSON internet tokens (JWT) used to imagine IAM roles. At present, when utilizing ASCP in Kubernetes, which assumes IAM roles by means of IAM roles for service accounts (IRSA), there’s a constraint in appending session tags throughout the IRSA assumption resulting from JWT declare restrictions, limiting the power to implement ABAC.
With ESO, you’ll be able to create Kubernetes Secrets and techniques and have your pods retrieve secrets and techniques from them as an alternative of instantly mounting secrets and techniques as volumes in your pods. ESO can also be able to utilizing its controller pod’s IRSA to retrieve secrets and techniques, so that you don’t have to arrange IRSA for every pod. You may as well function chain and specify secondary roles to be assumed by ESO IRSA and move session tags for use with ABAC insurance policies. ESO’s function chaining and ABAC capabilities assist lower the variety of IAM roles required for secrets and techniques retrieval. See Leverage AWS secrets and techniques shops from EKS Fargate with Exterior Secrets and techniques Operator on the AWS Containers weblog to learn to use ESO on an EKS Fargate cluster to devour secrets and techniques saved in Secrets and techniques Supervisor.
Conclusion
On this weblog publish, we walked you thru learn how to implement ABAC with Amazon EKS and Secrets and techniques Supervisor utilizing Exterior Secrets and techniques Operator. Implementing ABAC means that you can create a single IAM function for accessing Secrets and techniques Supervisor secrets and techniques whereas implementing granular permissions. ABAC additionally decreases your crew’s overhead and reduces the danger of misconfigurations. With ABAC, you require fewer insurance policies and don’t have to replace present insurance policies to permit entry to new companies and workloads.
When you have suggestions about this publish, submit feedback within the Feedback part beneath.
[ad_2]
Source link





